Regulatory Compliance Costs Too Much. We Heard You.
Address compliance and regulatory risks before they impact your business.
Empowering businesses to navigate the complexities of IT regulatory compliance with confidence and clarity.
Develop security programs.
Develop security and governance programs tailored to each client’s unique operational environment. These programs establish clear policies, procedures, and controls to address regulatory requirements and mitigate risks. By aligning security initiatives with business objectives, we create frameworks that are both effective and adaptable to evolving threats.
Identify vulnerabilities.
Assess risks and vulnerabilities by conducting comprehensive evaluations and to uncover hidden weaknesses in systems, processes, and data management practices.
Meet compliance mandates.
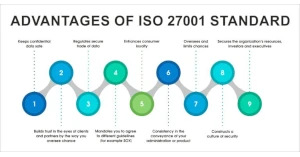
Meet security compliance mandates, such as PCI, HIPAA, GLBA, FISMA, GDPR, SOC and ISO 27001.
PARTNERING FOR SUCCESS
In a world where regulations evolve as fast as technology, staying compliant isn’t just a requirement—it’s a critical foundation for success.
In today’s regulatory landscape, compliance with frameworks like PCI-DSS, HIPAA, GLBA, FISMA, GDPR, SOC 2, and ISO 27001 isn’t optional—it’s essential for protecting your business and maintaining trust. These standards, whether addressing the security of payment systems, safeguarding personal health information, or ensuring the privacy of consumer and customer data, set the foundation for operational integrity in an increasingly interconnected world. From financial institutions to healthcare providers, and businesses managing sensitive data across borders, each regulation demands a precise approach tailored to the complexities of your industry.
Our deep understanding of these frameworks allows us to bring clarity and direction to even the most challenging compliance initiatives. Whether you’re navigating the stringent data protection mandates of GDPR, adhering to the audit and reporting standards of SOC 2, or aligning with ISO 27001 for comprehensive information security management, we provide the expertise to ensure your business is always prepared. In an environment where regulatory requirements continue to evolve, we help you remain confident, compliant, and secure.
ISO 27001 vs SOC 2 Certification: What’s the Difference?
Want to improve your data security but can’t decide between ISO 27001 and SOC 2? You’re in a familiar position.

Understanding the NIST Framework.
You may have heard about the NIST Cybersecurity Framework, but what exactly is it?
And does it apply to you?

What is the Gramm-Leach-Bliley Act?
The Gramm-Leach-Bliley Act requires financial institutions – companies that offer consumers financial products or services like loans, financial or investment advice, or insurance – to explain their information-sharing practices to their customers and to safeguard sensitive data.
Ready to start the conversation?
Our experts are here, ready to do what it takes to get the job done. Whether you’re a small business or a global enterprise.